Incoming Communication Record Audit – anamedeiro99, Anatarvasa, Asheshshyaam, axxin882, Babaijabeu, Business Ftasiastock, Dfqrbrb, Dhvlwlw, dianaandr3a, Doumneh
The incoming communication record audit for the listed stakeholders demands a methodical examination of each channel’s traceability and compliance. The approach must map data flows, control points, and accountability from origin to record, while enforcing data minimization and least-privilege access. It should produce auditable trails and precise remediation steps. Yet questions remain about scope, timing, and how to balance speed with governance, prompting a careful, skeptical assessment before proceeding.
What the Incoming Communication Record Audit Entails
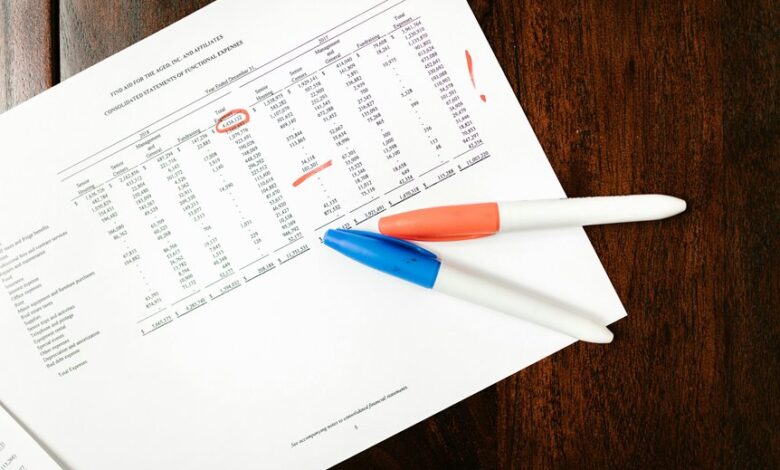
The Incoming Communication Record Audit entails a systematic examination of all inbound communications within a defined period, focusing on traceability, completeness, and compliance with established protocols.
Observations are methodical, skeptical, and free of presumption, emphasizing verifiable data lineage and potential compliance gaps.
Findings prioritize precise remediation, traceable accountability, and transparent controls, avoiding ambiguity while asserting auditable standards for ongoing freedom and governance.
How Each Stakeholder Channel Shapes Compliance and Transparency
Each stakeholder channel shapes compliance and transparency through distinct data flows, control points, and accountability mechanisms, requiring careful mapping to ensure traceability from origin to record.
The evaluation emphasizes data governance fundamentals, potential fragmentation, and audit trails; channels must align with overarching policy to sustain stakeholder transparency, minimize ambiguity, and empower freedom while preserving rigorous controls, verifiability, and balanced accountability across the enterprise.
Practical Steps to Audit Messages, Timing, and Access
Auditing messages, timing, and access requires a concrete, methodical approach that builds on the stakeholder-channel mapping discussed earlier. The process proceeds with an ethics review, documenting purpose and scope, then implementing data minimization to exclude unnecessary logs.
Privacy controls govern retention, access management enforces least privilege, and rigorous traceability ensures accountability while preserving freedom to audit openly and skeptically, without obstructive friction.
Best Practices to Safeguard Data While Maintaining Momentum
In safeguarding data while preserving momentum, organizations must balance rapid access with disciplined controls, questioning every access path, action, and exemption for necessity and proportionality.
The approach emphasizes data minimization and robust access controls, ensuring least privilege, ongoing verification, and auditable trails.
Skeptical scrutiny guards agility without sacrificing security, promoting transparent governance while preserving freedom to innovate within deliberate, purposeful boundaries.
Conclusion
The audit concludes with meticulous verification, meticulous documentation, meticulous accountability. It emphasizes traceability, traceability, traceability across origin, flow, and end record. It demands complete records, complete controls, complete access schemes. It enforces least-privilege, least-privilege, least-privilege at every juncture. It scrutinizes timing, timing, timing to prevent gaps. It expects transparent controls, transparent controls, transparent controls, and auditable trails, auditable trails, auditable trails, to sustain robust data stewardship.