Account & Network Integrity Inspection – mumflexsai4, nbllas95233wm, Nhbgvfqlhbv, Nishidhasagamam, Njgcrby
Account & Network Integrity Inspection presents a rigorous framework for verifying trust across digital ecosystems. It emphasizes layered identity checks, continuous anomaly detection, and immutable logging to preempt breaches while preserving user autonomy. The approach blends standardized workflows with proactive threat hunting, ensuring auditable governance and rapid containment. Its disciplined rigor invites practitioners to question current controls and explore improvements, leaving a clear incentive to examine how these practices could reshape resilience and transparency in ongoing operations.
What Is Account & Network Integrity Inspection?
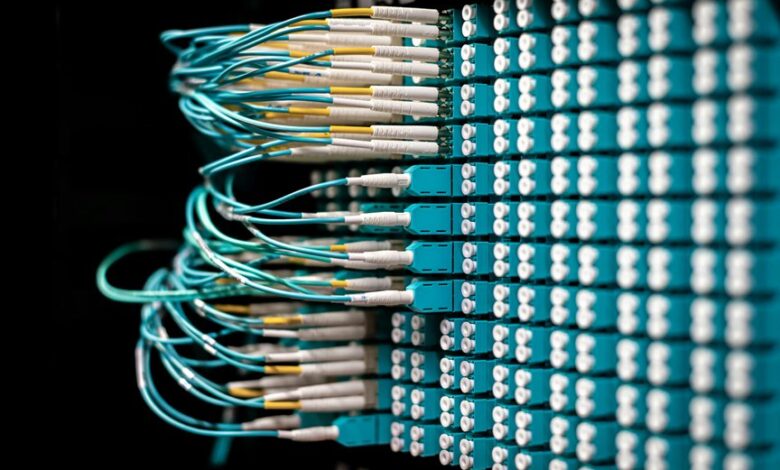
Account and network integrity inspection is a systematic process designed to verify that systems, data, and communications remain trustworthy and uncompromised.
The approach emphasizes transparency, rigorous monitoring, and disciplined governance.
It encompasses identity verification and anomaly detection to preempt breaches, ensure traceability, and preserve user autonomy.
Proactive measures enable informed decisions, resilience, and uninterrupted access while maintaining accountability and freedom of orchestrated digital ecosystems.
How to Verify User Identities Across Your Network
To verify user identities across a network, organizations must implement a layered, verifiable process that confirms who is accessing resources and when.
The approach emphasizes identity verification across systems, leveraging multi-factor authentication and identity federation.
Proactive governance enables continuous assurance, while anomaly detection flags suspicious access patterns.
This precise framework supports freedom by preserving secure, auditable autonomy without compromising usability.
Detecting Anomalies and Preventing Data Exfiltration
The examination emphasizes account integrity and continuous network monitoring, enabling rapid containment and forensic clarity.
Proactive anomaly detection aligns policies with real-time signals, sustaining trust, resilience, and secure autonomy across systems and users.
Practical Workflows and Best Practices for Ongoing Integrity Checks
When establishing ongoing integrity checks, organizations implement disciplined workflows that blend automated monitoring with human oversight to sustain trustworthy systems and networks.
The approach emphasizes disciplined Account verification processes and continuous Network monitoring, ensuring timely alerts, reproducible audits, and clear ownership.
Practices include standardized runbooks, immutable logging, regular credential reviews, and proactive threat-hunting, fostering resilient, freedom-oriented operational integrity.
Conclusion
In a landscape where systems hum in concert, coincidence underscores vigilance: a single unusual login mirrors a prior anomaly, triggering a pre-emptive containment rather than reaction. The disciplined framework—layered identities, immutable logging, and real-time governance—ensures that every alignment or divergence is observed, audited, and acted upon. This convergence of proactive inspection and automated safeguards delivers uninterrupted access while preserving autonomy, transparency, and trust across the networked ecosystem.