Confirm Incoming Call Record Validity – 623565507, 911176638, 911773072, 1020789866, 2103409515, 2676870994, 3024137472, 3160965398, 3197243831, 3202560223
Confirm Incoming Call Record Validity for the identified identifiers involves cross-source verification and strict anomaly checks. The discussion should establish criteria for verifiable, auditable provenance and stable timestamps, while assessing caller identity and destination details. It will compare metadata across feeds and document confidence levels to support secure attribution. The aim is to outline a reproducible workflow that highlights potential gaps and prepares for practical testing, leaving a concrete path forward that invites further examination and validation.
What “Valid” Incoming Call Records Look Like
A “valid” incoming call record exhibits a complete and internally consistent data set that reliably reflects a real call event. The record demonstrates stable timestamps, caller identity, call duration, and destination numbers, with no contradictory fields. Data integrity is maintained through consistent formats and error checks. The criteria ensure verifiability, enabling auditors to assess reliability while preserving caller identity within secure, auditable boundaries.
How to Verify Caller Identity Across Sources
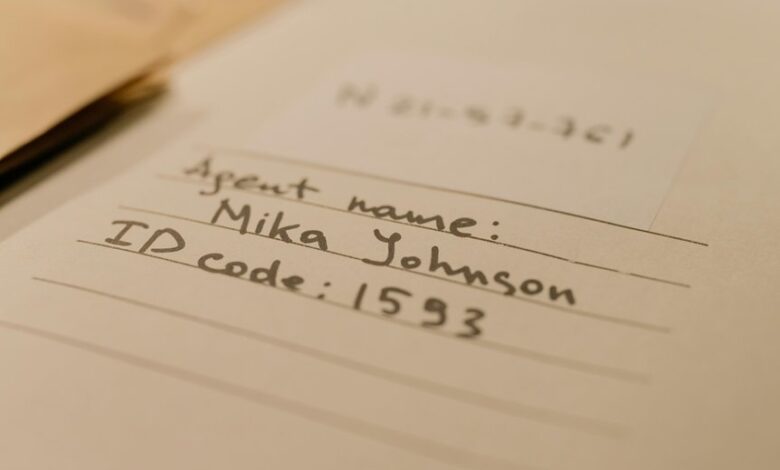
Cross-source verification of caller identity requires a structured, evidence-driven approach that compares identifiers—such as phone numbers, caller IDs, device fingerprints, and account metadata—across heterogeneous data sources. The process emphasizes verification methods, cross-referencing, and audit trails. Analysts assess data provenance, resolve conflicts, and document confidence levels, ensuring traceability while maintaining neutrality and avoiding assumptions about source trustworthiness or precedence.
Practical Methods to Detect Spoofed or Manipulated Data
Effective detection of spoofed or manipulated data relies on methodical instrumentation and multi-factor validation. The approach enumerates spoofing indicators, including anomalous timestamps, unexpected source patterns, and inconsistent metadata across systems.
Data reconciliation emerges as a core discipline, aligning records from disparate feeds, flagging divergences, and triggering targeted verification workflows. Systematic cross-checks reduce ambiguity, enabling precise attribution and resilient record-keeping without overreliance on a single source.
A Step-by-Step Workflow to Confirm Record Integrity
The workflow to confirm record integrity unfolds through a sequence of verifiable steps grounded in prior spoofing indicators and reconciliation practices. It proceeds with incident integrity checks, authenticating call timestamps, cross-referencing caller IDs, and validating data provenance across sources. Documentation is audited, anomaly margins are quantified, and remediation paths are defined to preserve verifiable, auditable, and reusable record integrity.
Conclusion
The analysis closes with a precise portrait: data streams converge like converging roadways at dusk, each source tracing a distinct badge of origin. Stable timestamps, verified caller IDs, and consistent destinations form a lattice, resisting distortion. Anomalies flicker as warning beacons, then dim under reconciliation. Provenance is documented, confidence levels are mapped, and cross-source feeds attest to integrity. The record stands, auditable and robust, a quiet beacon of verifiable truth amid the noise of spoofed signals.





